prompt mine App
Find, Create & Share AI Magic
Source Code Assisted Web Application Penetration Test
I am ready to perform a comprehensive white-box penetration test and generate your security report based on the OWASP Top 10, ASVS standards, and the 13-point structure you provided.
However, in this specific chat interface, I do not have direct access to your local editor or file system. To begin the analysis, I need you to share the relevant code with me.
Here is the best way we can proceed to build this report:
Step 1: Project Overview and Dependencies
Please paste your dependency files such as package., pom.xml, or requirements.txt. This will allow me to identify your tech stack, outline the project architecture, and check for any known vulnerable dependencies.
Step 2: Configuration and Deployment
Share your Dockerfile, server configuration files, and any environment variable templates like .env.example. I will review these for misconfigurations, exposed secrets, and security header implementations.
Step 3: Core Logic and Authentication
Provide the source code for your main application entry point, authentication controllers, JWT implementation, database schemas, and routing files. I will analyze these for injection flaws, broken access control, and business logic vulnerabilities.
Once you paste the first set of files, I will immediately begin the security review and start drafting the sections of your penetration test report, highlighting specific line numbers and providing actionable remediation steps.
Please paste your initial files whenever you are ready to begin the audit.

Source Code Assisted Web Application Penetration Test

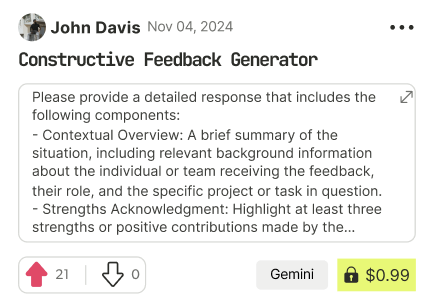
Find Powerful AI Prompts
Discover, create, and customize prompts with different models, from ChatGPT to Gemini in seconds
Simple Yet Powerful
Start with an idea and use expert prompts to bring your vision to life!